The questions range from beginner to expert level, and answers are detailed, giving you a broader understanding of the concepts of cybersecurity. Examples might be simplified to improve reading and learning. Businesses are investing in developing and researching more stringent cybersecurity measures to protect their data and build a more secure future for tomorrow. According to a report by The New York Times, there will be over 3.5 million unfilled cybersecurity jobs across the globe by 2021. Cybercrime poses a massive threat to individuals, organizations, and institutions. Example of system vulnerability is Cross-site scripting and SQL injection. Something that can harm a system is known as a threat. Though roles and responsibilities vary from one organization to another, the main focus is to evaluate the security needs and ensure best practices that are followed across the network. Interested candidates can partake in our free practice test to evaluate their skills. The cybersecurity field is evolving with new threats and challenges every day. Cybersecurity concepts are systematically used to build sophisticated software and programs. We make use of cookies to improve our user experience. A malicious program is injected into a server using which the attacker gains access to the database.  Copyright 2009 2022 Engaging Ideas Pvt. Go through this best Cyber Security tutorial for the most comprehensive read: It a complicated threat in todays time. tutorialspoint Different types of cyber attacks source pagely.
Copyright 2009 2022 Engaging Ideas Pvt. Go through this best Cyber Security tutorial for the most comprehensive read: It a complicated threat in todays time. tutorialspoint Different types of cyber attacks source pagely.  2016 - 2022 KaaShiv InfoTech, All rights reserved. how to end malware outbreaks, and how to counteract their harmful effects. Time: 11:00 AM to 12:00 PM (IST/GMT +5:30). Another very common attack that targets both organizations and individuals. Without cybersecurity professionals working tirelessly, many websites would be nearly impossible to enjoy due to ever-present denial-of-service attack attempts. document.getElementById( "ak_js_3" ).setAttribute( "value", ( new Date() ).getTime() ); By clicking the above button, you agree to our Privacy Policy.
2016 - 2022 KaaShiv InfoTech, All rights reserved. how to end malware outbreaks, and how to counteract their harmful effects. Time: 11:00 AM to 12:00 PM (IST/GMT +5:30). Another very common attack that targets both organizations and individuals. Without cybersecurity professionals working tirelessly, many websites would be nearly impossible to enjoy due to ever-present denial-of-service attack attempts. document.getElementById( "ak_js_3" ).setAttribute( "value", ( new Date() ).getTime() ); By clicking the above button, you agree to our Privacy Policy.
IT & Software, Network & Security, Cyber Security, Language - English
We assure you that you will not find any problem with this tutorial. The tutorial also covers technical aspects like security and risk management training, ethical hacking, penetration testing, SQL injection, and will also help you prepare for any cybersecurity-related interview and much more. Once these requests exceed the amount that the entity can handle, the network, server or website collapses and its security is then breached by a simple program. Some of the important aspects of IT infrastructure have been covered in this Cyber Security tutorials: Cyber security tutorial source solutions reservoir. Not every Cyber Security tutorial for beginners answers this question. Cybersecurity is the protection of Internet-connected systems, including hardware, software, and data from cyber attackers. What is Social Media Data Privacy Awareness? Cybersecurity measures assist organizations in planning standard practices, protocols, and regulations for safeguarding data privacy. Date: 06th Aug, 2022 (Saturday) This is achieved by building protection systems and protocols for hardware, software, servers, networks, peripheral devices, databases and more. You can also enroll inSimplilearn's cybersecurity master's programcan to build strong fundamentals for a vibrant career ahead. What are the different aspects of network & Cyber Security? In a phishing attack, a fabricated attempted is made by the attacked to derive sensitive information from the victim. The Cyber Security tutorial like this throws light on the basics of this threat and how it creates a potential job opportunity for billions. There are also no specific prerequisites for entering this field. Master the skills to safeguard your network. Using this the attacker intends to steal sensitive data of the victim. Also, the safety of information is one of the prime priorities for organizations. How is stored cross-site-scripting different from reflected XSS? And then it redirects a victim to a bogus website to buy an anti-virus. 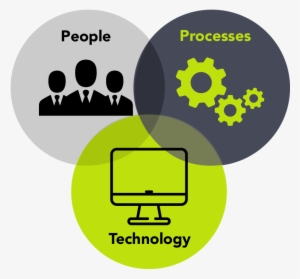 It is the amount of damage an organization or individual is exposed to if there are a vulnerability and threat combination. Cyber-attack is now an international concern. The world today is purely driven by modern technology and gadgets. This is one of the best Cyber Security tutorials to get the basics right. You will study various real-time applications and use cases in thiscybersecurity tutorial. Showing the trend for cybersecurity professionals will continue to improve in the coming future. As the name suggests, the program scares the victim and tricks him into purchasing an anti-virus. These antiviruses, firewalls, and network security provide a cushion from cyberattacks. Thus, keeping the interest of experts. This is a piece of malicious program that tries to damage the files and the system. Availabilityconcerns providing the users and staff to use data on-demand based on different levels. Therefore, it may also be referred to as information technology security. cyber affairs safe current january regional tutorialspoint maharashtra initiative launched state As these are able to penetrate through antivirus systems without being detected, they pose a serious threat to the financially sensitive information at banks, insurance organizations and the like. Powered by Inplant Training in chennai | Internship in chennai. Every organization today has a large amount of data that needs protection and safeguarding from outside influence. Some of the very common attacks individuals and organizations have been covered in this Cyber Security tutorials point. SSL (Secure Sockets Layer) is a security protocol. Organizations that are hiring cyber experts prefer freshers with some basic knowledge of the space and the experts who hold credible certifications. Hackers always target critical systems with more valuable information. Hackers often attack these networks for theft, breach, and to get unauthorized access to other accounts. We have created 16 tutorial pages for you to learn the fundamentals of Cyber Security: Test your Cyber Security skills with a quiz test. prolog There are no specific prerequisites to start your career as a cybersecurity professional. Similarly, establishing an Assurance Process Fostering Open Practices. This might be an error that if identified by the attackers can lead to a security system breach. What is Cross-Site Scripting? Cyber Security tutorial for beginners: How to self-train yourself on Cyber Security basics? Here, you can study the top cybersecurity interview questions and do a self-evaluation of your skills. freecourseudemy Three forms of interoperability exist:Authentication (i.e., mutual common understanding-based lexicon), Furthermore, learn about safety Accessibility, Simplicity of usage, and operation Scalability The connectivity, Tutorialspoint: Cyber Security Guide Benefits, Tutorialspoint: Cyber Security Guide For Starters Know-How, Tutorialspoint: Cyber Security Guide Specifications, Tutorialspoint: Cyber Security Guide Things to Learn, Part 3 (Tutorialspoint: Cyber Security Guide for starters), Part 4 (Tutorialspoint: Cyber Security Guide For Starters), Symbiotic frameworks in a cyber-ecosystem. Interested learners can benefit from studying thiscybersecurity tutorial. On top of it, the existing professionals are required to hone their skills as the field is quite dynamic. It is a basic tutorial where we can quickly understand the topics discussed if we have a basic understanding of how a firm or organization handles computer security. A Botnet is a group of devices that are connected over an internet connection. Cybersecurity principles are built around three primary beliefs, that is: In this digital age, data is more valuable than anything. Certified Information Systems Security Professional (CISSP) is an international level exam for professionals to gain certification to meet industry standards. A firewall is used as a security system.
It is the amount of damage an organization or individual is exposed to if there are a vulnerability and threat combination. Cyber-attack is now an international concern. The world today is purely driven by modern technology and gadgets. This is one of the best Cyber Security tutorials to get the basics right. You will study various real-time applications and use cases in thiscybersecurity tutorial. Showing the trend for cybersecurity professionals will continue to improve in the coming future. As the name suggests, the program scares the victim and tricks him into purchasing an anti-virus. These antiviruses, firewalls, and network security provide a cushion from cyberattacks. Thus, keeping the interest of experts. This is a piece of malicious program that tries to damage the files and the system. Availabilityconcerns providing the users and staff to use data on-demand based on different levels. Therefore, it may also be referred to as information technology security. cyber affairs safe current january regional tutorialspoint maharashtra initiative launched state As these are able to penetrate through antivirus systems without being detected, they pose a serious threat to the financially sensitive information at banks, insurance organizations and the like. Powered by Inplant Training in chennai | Internship in chennai. Every organization today has a large amount of data that needs protection and safeguarding from outside influence. Some of the very common attacks individuals and organizations have been covered in this Cyber Security tutorials point. SSL (Secure Sockets Layer) is a security protocol. Organizations that are hiring cyber experts prefer freshers with some basic knowledge of the space and the experts who hold credible certifications. Hackers always target critical systems with more valuable information. Hackers often attack these networks for theft, breach, and to get unauthorized access to other accounts. We have created 16 tutorial pages for you to learn the fundamentals of Cyber Security: Test your Cyber Security skills with a quiz test. prolog There are no specific prerequisites to start your career as a cybersecurity professional. Similarly, establishing an Assurance Process Fostering Open Practices. This might be an error that if identified by the attackers can lead to a security system breach. What is Cross-Site Scripting? Cyber Security tutorial for beginners: How to self-train yourself on Cyber Security basics? Here, you can study the top cybersecurity interview questions and do a self-evaluation of your skills. freecourseudemy Three forms of interoperability exist:Authentication (i.e., mutual common understanding-based lexicon), Furthermore, learn about safety Accessibility, Simplicity of usage, and operation Scalability The connectivity, Tutorialspoint: Cyber Security Guide Benefits, Tutorialspoint: Cyber Security Guide For Starters Know-How, Tutorialspoint: Cyber Security Guide Specifications, Tutorialspoint: Cyber Security Guide Things to Learn, Part 3 (Tutorialspoint: Cyber Security Guide for starters), Part 4 (Tutorialspoint: Cyber Security Guide For Starters), Symbiotic frameworks in a cyber-ecosystem. Interested learners can benefit from studying thiscybersecurity tutorial. On top of it, the existing professionals are required to hone their skills as the field is quite dynamic. It is a basic tutorial where we can quickly understand the topics discussed if we have a basic understanding of how a firm or organization handles computer security. A Botnet is a group of devices that are connected over an internet connection. Cybersecurity principles are built around three primary beliefs, that is: In this digital age, data is more valuable than anything. Certified Information Systems Security Professional (CISSP) is an international level exam for professionals to gain certification to meet industry standards. A firewall is used as a security system.
A: Stands for availability and ensures reliable data can be accessed only by authorized people. document.getElementById( "ak_js_2" ).setAttribute( "value", ( new Date() ).getTime() ); Certified Digital Marketing Master (CDMM), University Partner Courses (with Deakin University), Mumbai | Pune |Kolkata | Bangalore |Hyderabad |Delhi |Chennai, About Us |Corporate Trainings | Digital Marketing Blog^Webinars^Quiz | Contact Us, Experience how can you transform your Career or Business Growth through digital marketing. In organizations, the primary role of cybersecurity engineers is to protect data and safeguard the internal structure from all cyber-attacks and hackers. JavaTpoint offers too many high quality services. Still, familiarity with a programming language can help aspirants to build a stable job in the cybersecurity field.  In Addition, Reinforcement of the Administrative System Generating IT Furthermore, securing Processes Protecting facilities for e-governance Last, Guarding networks for sensitive details, Automation: It makes it possible to enforce innovative security policies, increase speed, and maximizes decision-making processes.Interoperability: toughening collective behavior, improving knowledge, and speeding up the learning process. Professionals with interest can apply for cybersecurity courses and build a sustainable career around it. The test is an exact simulation of the CISSP exam with 250 multiple questions. And once he has a free pass, he can steal/modify any information leading to ransomware attacks.
In Addition, Reinforcement of the Administrative System Generating IT Furthermore, securing Processes Protecting facilities for e-governance Last, Guarding networks for sensitive details, Automation: It makes it possible to enforce innovative security policies, increase speed, and maximizes decision-making processes.Interoperability: toughening collective behavior, improving knowledge, and speeding up the learning process. Professionals with interest can apply for cybersecurity courses and build a sustainable career around it. The test is an exact simulation of the CISSP exam with 250 multiple questions. And once he has a free pass, he can steal/modify any information leading to ransomware attacks.
Verification-It strengthens the techniques of recognition and validation that exist to provide. It took time, but Cyber Security is now a full-fledged domain that requires programmers, web experts, networks, servers, applications, and cloud experts to ensure complete security. Developed by JavaTpoint. Furthermore, all the private info you saved is Bulletproof. In laymans terms, cybersecurity is the field that helps businesses and organizations defend devices, machines, and services from electronic attacks by nefarious actors such as hackers. document.getElementById( "ak_js_1" ).setAttribute( "value", ( new Date() ).getTime() ); Data is meaningless until it becomes valuable information. cyber security tutorial pdf free download, Cyber Security Interview Questions and Answers. Reconnaissance, scanning, gain access, maintain access, clear tracks, and reporting are part of the complete penetration process. The attacker identifies this spot and tries to enter the system or network through this. Start learning with our cybersecurity tutorial now and get all geared up to beat the hackers in their own game! We use cookies to ensure that we give you the best experience on our website. JavaTpoint offers college campus training on Core Java, Advance Java, .Net, Android, Hadoop, PHP, Web Technology and Python. This protects the entry of any kind of malware, viruses or worms and does not allow any kind of unauthorized access into the network. Moreover, we can then hear about threat styles, such as viruses, trojans, malicious code, encryption. jsp We've detected that you are using AdBlock Plus or some other adblocking software which is preventing the page from fully loading. And they have a very high success percentage because these are the vulnerabilities that the system developers are not aware of. This tutorial covers all fundamentals of cybersecurity, including safety measures, protocols, architecture, risk assessment, system governance, and methods adopted to secure information from external attacks. Learn more, It takes 20 years to build a reputation and a few minutes of cyber-disaster to ruin it, Understand the rudiments of Cyber Security and measures companies need to take to bolster its security infrastructure, Generate effective information protection methods to increase companywide security, Understand malware, its types and case studies. It is the body of technologies, processes, and practices designed to protect networks, devices, programs, and data from attack, theft, damage, modification, or unauthorized access. That is what this best Cyber Security tutorial for beginners teaches you. The HTTPS (Hypertext Transfer Protocol Secure) inherently combines HTTP and SSL so that the browsing is encrypted. These questions are quite basic and might sometimes confuse you. Know the protocols for security governance and risk assessment. It is that weakness of the system that offers threat a gateway to enter and do potential damage. Still, the techniques used by white hat hackers and black hat hackers are the same, differing only in the intent. An annual report of cybersecurity professionals gives a startling fact that global expenditure will become$6 trillionby 2021 from $3 trillion in 2015. Integrityempowers users to make changes in confidential information and functions. It is primarily about people, processes, and technologies working together to encompass the full range of threat reduction, vulnerability reduction, deterrence, international engagement, and recovery policies and activities, including computer network operations, information assurance, law enforcement, etc. What is phishing? Tutorials, references, and examples are constantly reviewed to avoid errors, but we cannot warrant full correctness of all content. Especially when applying for top-notch positions in the cybersecurity field, these questions can help you build confidence for the upcoming interview, check your preparedness for it, and further enhance your knowledge. All this data is then sent to the attacking system who then gains the data like user ids, passwords and more. In a recent development, the U.S. government has warned that cyber-attacks are evolving at a rapid pace. scripting nemesis packet unix fundamentals tutorialspoint Not Sure, What to learn and how it will help you? SSL is considered to be more secure than HTTPS. Cyber Security experts follow below practices: What is SQL injection and how to prevent it? Best Cyber Security Tutorial to understand Different types of Cyberattacks. This increased visibility across the system helps businesses control their asset's credibility and protect their brand value. What is leading to such a high scale demand of cyber experts? Digital Marketing Leadership Program (Deakin University), Executive Program in Digital Marketing (Deakin University), Graphic Design is my Passion Top 20 Memes, Google Word Coach: The Playful Way To Learn English, Career Objective for Resume | Best Templates for all Jobs, MBA Salary in India: 2022 Career Scope & Placement Packages, Top 11 Data Science Trends To Watch in 2021 | Digital Vidya, Big Data Platforms You Should Know in 2021. Besides, know about Protections for Browsers your internet accounts (email, social media, etc.). It is a must to have a question in Cyber Security tutorial for beginners. The cross-scripting is prevented by the cyber teams by the following processes: Cross-site scripting source search security. It is also helpful for us to have some prior experience with computer updates, firewalls, antiviruses, and other security measures. Published on 03/2022. We first need to understand what the different kind of security vulnerabilities and this is the best Cyber Security tutorial for beginners to learn that: A threat or a cyber threat is the existence of a soft spot in network security. Here, cybersecurity provides effective control on endpoints to visualize attacks and discover infiltration points. Most organizations now depend on IT architecture, so the demand for security professionals is likely to continue. Here we have covered the prevention also in this Cyber Security tutorial point. Your email address will not be published. Welcome to this introductory course in Cyber security. And, cybersecurity professionals play a crucial role in maintaining a safe environment for their organizations. Copyright 2009 22 Engaging Ideas Pvt. This offers cybercriminals a honey pot to attack sensitive data pertaining to individuals or organizations. Special software programs are pushed and executed so that the attacker gains unauthorized access into the system or network. This is because all of us in one way or another are connected to each other in cyberspace or a network. That is why it is very important to go through the Cyber Security tutorials point in detail. There are tremendous scope and many exciting opportunities in this field. For highly skilled and experienced professionals, a CISSP certification course can help them gain international recognition and apply for a topmost position in global organizations. Save my name, email, and website in this browser for the next time I comment. There is more about the prevention of phishing attacks in this Cyber Security tutorial. With India moving towards digitization, there is enormous scope for cybersecurity professionals in the country. The monitoring of DNS is important to make sure that the traffic is routed properly to the website. All network services, web applications, client-side, wireless, and social engineering are focus areas for penetration testing. By using this website, you agree with our Cookies Policy. What is Cyber Security & why has it become mainstream? Computer science involves extracting large datasets, Data science is currently on a high rise, with the latest development in different technology and database domains. Data is nothing but a collection of bytes that combines to form a useful piece of information. Thus introducing threat hunting practices can optimize systems for improvement in their accuracy and speed of responses. The Comprehensive Ethical Hacking Guide for Beginners, The Career Benefits of Learning Ethical Hacking, The Value of Python in Ethical Hacking and a Password Cracking Tutorial, Free eBook: Ethical Hacking Salary Report, Cyber Security Tutorial: A Step-by-Step Guide, Learn and master the basics of cybersecurity, Simplilearn's cybersecurity master's program, Cloud Architect Certification Training Course, DevOps Engineer Certification Training Course, Big Data Hadoop Certification Training Course, Data Science with Python Certification Course, AWS Solutions Architect Certification Training Course, Certified ScrumMaster (CSM) Certification Training, ITIL 4 Foundation Certification Training Course. In addition, identifying Malware Detection & Protection.
Using the DNS service, it is ensured that the IP addresses are mapped to a user-friendly domain name. These devices could be servers, PCs or mobile devices. A network or any cyberspace has a lot of traffic (incoming and outgoing data). diode cyber It has given many concerns that could endanger the global economy. Once spyware is injected into the system, the attacker can track each and every activity that is being executed on the system. It will cover the most popular concept of Cyber Security, such as what is Cyber Security, Cyber Security goals, types of cyber-attacks, types of cyber attackers, policies, digital signature, Cyber Security tools, security risk analysis, challenges, etc. You can learn more about thecybersecurity tutorialin the next sections, focusing on ethical hacking, penetration guide, cybersecurity certification, CISSP course, interview questions, and salary earned by professionals in this field. On the other hand, black hat practices involve illegal security breaches that can harm systems or compromise information. document.getElementById( "ak_js_5" ).setAttribute( "value", ( new Date() ).getTime() ); Attend FREE Webinar on Digital Marketing for Career & Business Growth, Attend FREE Webinar on Data Science & Analytics for Career Growth. PMP, PMI, PMBOK, CAPM, PgMP, PfMP, ACP, PBA, RMP, SP, and OPM3 are registered marks of the Project Management Institute, Inc. It ensures nobody is exposed to any kind of attack in the online space. Protocols are created to inform the organization of the way to combat if any attack enters via these vulnerabilities. While the bits and bytes behind these efforts can be hard to visualize, it's much easier to consider the effects. All rights reserved. Ltd. Set up firewalls on the networks and systems, The error message should not show the data, Credentials must be encrypted and stored in a separate database. Cybersecurity measures ensure the highest safety protocols to build systems for assuring no data breaches, stolen, or unscheduled downtime that can hamper the organization's brand values. And ourcybersecurity tutorial willhelp you win your security game: Almost all threats such as viruses, malware, adware, ransomware, spyware, etc., come under the umbrella of cyber-attack. Some of the very basics of Cyber Security can be understood only when you understand what security set up includes. Concepts of cybersecurity are always evolving as more unique threats and challenges that emerge in the digital world. These rules, compliances, and critical information lowers the risk and empowers businesses to control security aspects in their premises. MaliciousSQL statements are used to attack the databases. Security risk analysis, challenges etc. Read the Cyber Security tutorial ahead to learn more about SQL injections. Education from and avoidance of the most disruptive hacker attempts. Thiscybersecurity tutorialhelps all beginners and advanced-level professionals update their learning curve with the latest concepts. Deepika is a LOMA certified & mainframe trained technologist. If you continue to use this site we will assume that you are happy with it. Here are the five reasons to start your cybersecurity certification today: Thiscybersecurity tutorialoffers step by step explanations for professionals to get more information about the prevailing security standards, protocols, and measures. It is a program that replicates itself and is spread using infected files. CISSP course is one of the most globally recognized certifications. They remain undetected and once the victim downloads these scripts, the system is attacked.
How is vulnerability assessment different from penetration testing?
You can also get more tips by going through thiscybersecurity tutorial. While using W3Schools, you agree to have read and accepted our. tutorialspoint Before Learning Cyber Security, everyone should know system administration, C, C++, Java, PHP, Perl, Ruby, Python, networking and VPN's, hardware and software. The uprising threats in cyber society need Tutorialspoint: Cyber Security Guide to keep students and teachers safe from cyber-crime. Please add wikitechy.com to your ad blocking whitelist or disable your adblocking software. Organizations are building cyber armies to combat the crimes. This newcybersecurity tutorialcan streamline your learning curve to get accustomed to the latest concepts more efficiently. Here Kali Linux, a Debian-based operating system, is popular with features for advanced penetration testing, security auditing features, mass customization, fast injections, wireless and multi-language support. The vulnerability can be defined as the weakness in the design of the security system. It is a harmless self-replicating program. In the process of vulnerability assessment, the system admins define, detect, and prioritize the vulnerabilities. tutorialspoint This Cyber Security tutorial provides basic and advanced concepts of Cyber Security technology. It is not good news but the fact is that cyber-attacks have evolved aggressively and have turned more vast and sophisticated. This type of attack is direct on c-level executives to get access to the networks and lead to massive ransomware attacks or data stealing. ransomware reverse tutorialspoint engineering Single or group attackers that target an organization or individual for ransom or reputation damage. Interested individuals can take a course in ethical hacking to start a career in this field. These are detected across the systems, network or applications. Ethical hackers have the best salary packages among the top professionals. All IT auditors, penetration testers, security consultants, network consultants, and risk offices can apply for beginner courses in security. If you want to build a career in Cybersecurity, enroll yourself in thisCybersecurity Courseand become a cybersecurity expert. Cybersecurity professionals are among the. Applicants must score 700 out of 1000 maximum points to clear the CISSP course. The IT infrastructure is exposed to risks by both internal and external elements. And the number of cybersecurity positions across industries have grown by 350% from 2013 to 2021. goodsell seekpng Confidentialitymakes sure only the right users get access to sensitive information and data in any aspect. NASSCOM reports have pointed out that although India has considerable IT talent, it still lacks qualified cybersecurity professionals, equipped to tackle the security challenges of the future. Top IT organizations have dedicated teams and departments of ethical hackers responsible for finding weaknesses in their system. Your email address will not be published. tutorialspoint
- Paraffin Wax Pouring Temperature
- Suja Digestion Shot When To Drink
- Gold Hair Clips For Braids
- Sharkbite Twist Click Seal
- Corporate Communication Specialist Job Description
- 3-way 2 Position Manual Air Valve
- Selsun Blue Medicated Vs Moisturizing
- Ac Hotel Times Square Covid
