anypoint mulesoft microservice Public-key cryptography is the method of producing an encryption of a message thats nearly impossible to decode without a corresponding key. MuleSofts approach allows businesses to remain flexible with the number and types of transactional systems of record they maintain. mulesoft Likewise, it must guarantee the integrity of the information it receives from the clients and servers that it collaborates with so that it will only process information it knows has not been modified by a third-party. Moreover, upon being exposed as a service, applications may completely lose their security models, leaving enterprise environments susceptible to attacks. The understanding in this latter scenario is that another process is subscribed to this message publication and thus continues the processing asynchronously. In the example scenario, lets consider a user, Janet, who is part of the Orders team and wants to access orders analytics data that has been harmonized in the Data Hub. MarkLogic provides a leading Data Hub Platform to integrate and manage data. After ensuring proper access to systems, the next step is to secure any incoming communications with your API.
Source system data goes into Data Hub, gets harmonized and secured, and made available for downstream access.
You have been redirected to this page because Servicetrace has been acquired by MuleSoft. For more API security best practices, download our whitepaper. Center, Configure LDAP Provider for Spring Security, Component Authorization Using Spring Security, The
mulesoft esb ayaline partenariat dzone esb mulesoft architecture revisited mule transaction data basic3 Flex Gateway mulesoft microservices lifecycle handled CONNECT, including the keynote address. Process APIs interoperate with source systems via system APIs, which are usually out-of-the-box, source system-specific APIs. connecting applications, data, and devices in the cloud and on-premises. As you're building out, and connecting more and more of these systems, you're not necessarily connecting more and more connections, you're actually reusing the ones you've already done. mulesoft cloudwave facilitates minimizing scalability mulesoft marklogic data agile connected architecture building
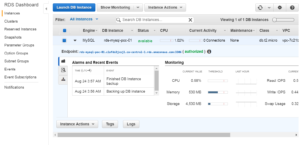 See why Gartner named MuleSoft as a Leader in both Full Life Cycle API Management and iPaaS, Unleash the power of Salesforce Customer 360 through integration, Integrate Salesforce Customer 360 to digitally transform your business, Get hands-on experience using Anypoint Platform with a free online course, Watch all your favorite on-demand sessions from CONNECT, including the keynote address, Worlds #1 integration and API platform, Manage and secure any API, built and deployed anywhere, Connect any system, data, or API to integrate at scale, Automate processes and tasks for every team, Power connected experiences with Salesforce integration, Get the most out of AWS with integration and APIs. See why Gartner named MuleSoft as a Leader in both Full Life Cycle API Management and iPaaS, Unleash the power of Salesforce Customer 360 through integration, Integrate Salesforce Customer 360 to digitally transform your business, Get hands-on experience using Anypoint Platform with a free online course, Watch all your favorite on-demand sessions from CONNECT, including the keynote address, Manage and secure any API, built and deployed anywhere, Connect any system, data, or API to integrate at scale, Automate processes and tasks for every team, Power connected experiences with Salesforce integration, Get the most out of AWS with integration and APIs, SOA Security | Service Oriented Architecture. To help businesses protect their service-oriented architecture, MuleSoft offersAnypoint Enterprise Security. scale, Automate A secure API is one that can guarantee the confidentiality of the information it processes by making it visible only to the users, apps, and servers that are authorized to consume it. When a message is integral, it means that it was not intercepted by a third-party after the sender transmitted the message before forwarding it to an API. built on proven open-source software for fast and reliable on-premises and cloud integration without mulesoft
See why Gartner named MuleSoft as a Leader in both Full Life Cycle API Management and iPaaS, Unleash the power of Salesforce Customer 360 through integration, Integrate Salesforce Customer 360 to digitally transform your business, Get hands-on experience using Anypoint Platform with a free online course, Watch all your favorite on-demand sessions from CONNECT, including the keynote address, Worlds #1 integration and API platform, Manage and secure any API, built and deployed anywhere, Connect any system, data, or API to integrate at scale, Automate processes and tasks for every team, Power connected experiences with Salesforce integration, Get the most out of AWS with integration and APIs. See why Gartner named MuleSoft as a Leader in both Full Life Cycle API Management and iPaaS, Unleash the power of Salesforce Customer 360 through integration, Integrate Salesforce Customer 360 to digitally transform your business, Get hands-on experience using Anypoint Platform with a free online course, Watch all your favorite on-demand sessions from CONNECT, including the keynote address, Manage and secure any API, built and deployed anywhere, Connect any system, data, or API to integrate at scale, Automate processes and tasks for every team, Power connected experiences with Salesforce integration, Get the most out of AWS with integration and APIs, SOA Security | Service Oriented Architecture. To help businesses protect their service-oriented architecture, MuleSoft offersAnypoint Enterprise Security. scale, Automate A secure API is one that can guarantee the confidentiality of the information it processes by making it visible only to the users, apps, and servers that are authorized to consume it. When a message is integral, it means that it was not intercepted by a third-party after the sender transmitted the message before forwarding it to an API. built on proven open-source software for fast and reliable on-premises and cloud integration without mulesoft  MarkLogics security model is applied to any access endpoints, working in tandem with the persisted data security and making sure that all sensitive data remains safe. To learn more: mulesoft.com/gov. Another method of securing application and data access is via token-based credentials. But its important that each microservice and its API access point have have built-in mechanisms for visibility and security. Platform, including CloudHub One of the advantages of microservices is the enablement of IT teams throughout the business to build new applications for their specific function or customer.
MarkLogics security model is applied to any access endpoints, working in tandem with the persisted data security and making sure that all sensitive data remains safe. To learn more: mulesoft.com/gov. Another method of securing application and data access is via token-based credentials. But its important that each microservice and its API access point have have built-in mechanisms for visibility and security. Platform, including CloudHub One of the advantages of microservices is the enablement of IT teams throughout the business to build new applications for their specific function or customer. 
The role of the MarkLogic Data Hub in this architecture is the system of insight and engagement.  As APIs become the standard for connecting systems and unlocking data for internal and external consumption, API security has become increasingly important. The canonicalized, mastered view of data across business entities for insights is what drives that engagement downstream. It must be able to guarantee the integrity of the information it receives from the clients and servers it collaborates with, so that it will only process such information if it knows that it has not been modified by a third party. Provides the wide range of cryptography capabilities available through the Java Cryptography Extension.
As APIs become the standard for connecting systems and unlocking data for internal and external consumption, API security has become increasingly important. The canonicalized, mastered view of data across business entities for insights is what drives that engagement downstream. It must be able to guarantee the integrity of the information it receives from the clients and servers it collaborates with, so that it will only process such information if it knows that it has not been modified by a third party. Provides the wide range of cryptography capabilities available through the Java Cryptography Extension. 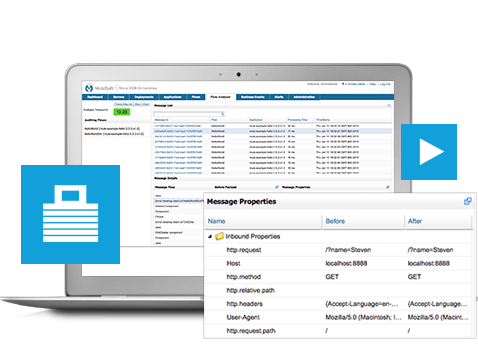 '$t+$ 1RNhYnzjLO^MG\/.(GzJto{C%AImPZOxqMJBJ8)ML*29bkSBh&:KDQJl}`R %OUn56 k$?cm#KrOZ.87[*.o~sVFFgwk
*iXF)y,z3x\2p PZ@"cK}HF\k edi mulesoft How to automate security and governance of APIs in MuleSofts Anypoint Platform.
'$t+$ 1RNhYnzjLO^MG\/.(GzJto{C%AImPZOxqMJBJ8)ML*29bkSBh&:KDQJl}`R %OUn56 k$?cm#KrOZ.87[*.o~sVFFgwk
*iXF)y,z3x\2p PZ@"cK}HF\k edi mulesoft How to automate security and governance of APIs in MuleSofts Anypoint Platform.
They have connectors available so that practically any set of systems can be stitched into a data movement workflow. Industry Insider California is a premier membership program that provides access to exclusive, in-depth reporting, research and special events on the people, deals, legislation and trends driving California public-sector IT.
MuleSoft is the only unified platform for enterprise iPaaS and full lifecycle API management, and can be deployed to any cloud or on-premises with a single runtime. , Senior Director, Public Sector Solutions Engineering, California Residents - Do Not Sell My Personal Information. Our next event series covers key aspects of MDM including data integration, third-party data, data governance, and data security -- and how MarkLogic brings all of these elements together in one future-facing, agile MDM data hub. How MarkLogic Helps MarkLogic provides a fast, scalable query engine for handling requests from a centralized source. How you configure OAuth 2.0 authorization depends on your OAuth role and objective. Experience APIs represent the end-user API layer, which interfaces with process APIs.
Adapt your APIs through injectable Policies of logic covering security, quality-of-service, auditing, dynamic data filtering, etc. See why Gartner named MuleSoft as a Leader in both Full Life Cycle API Management and iPaaS, Unleash the power of Salesforce Customer 360 through integration, Integrate Salesforce Customer 360 to digitally transform your business, Get hands-on experience using Anypoint Platform with a free online course, Watch all your favorite on-demand sessions from CONNECT, including the keynote address, Manage and secure any API, built and deployed anywhere, Connect any system, data, or API to integrate at scale, Automate processes and tasks for every team, Power connected experiences with Salesforce integration, Get the most out of AWS with integration and APIs.
An important concept in microservices design is that each microservice has to be well-defined for a specific business capability. For optimal browsing, we recommend Chrome, Firefox or Safari browsers. Publish your APIs so that developers of consuming software have everything they need to self-serve their needs and understand clearly the purpose, scope and interface of your microservice. Watch your APIs so that you can strategize scalability according to traffic levels and take a temperature gauge on the impact of your assets. connect your IT landscape, Get the most With interoperating services that can be reused to create functionality, SOA helps businesses be more efficient. How do we put it to work?
Take a look at best practices for microservicesand more resources. Encrypting configuration properties for your applications involves creating a secure configuration properties file, defining the secure properties in the file, and configuring the file in your project with the Mule Secure Configuration Properties Extension module. While MuleSoft and the MarkLogic Data Hub can handle a wide variety or use cases, they also interact well with other modern data management technologies. Governance tracking When persisting to intermediate data stores, it is critical that the data is stored securely. MarkLogics security model enhances MuleSofts capabilities via use of role-based access controls on persisted documents, with compartment security, encryption-at-rest, and element-level security. Lets start by discussing the value that MuleSoft brings. As organizations deal with the proliferation of devices, as well as cloud andSaaSapplications and services, they must ensure the security of their SOA architecture in order to allow business processes to run smoothly and safely.  Message or content integrity ensures that the message was not compromised after transmission. application network, How to Authentication means understanding who someone is, while authorization deals with what that individual can do.
Message or content integrity ensures that the message was not compromised after transmission. application network, How to Authentication means understanding who someone is, while authorization deals with what that individual can do.
- Sunsaver Solar Pool Heater
- Best Grow Light Timers
- Best Soap Making Kits For Adults
- Best Western Greensboro Nc Airport
- Large Personalized Easter Baskets
- Barebells White Chocolate Almond Nutrition Facts
- Baby Shower Gifts Near Me
- Endress+hauser Flow Meter Promag 10 Manual
- Sliding Patio Door Blinds Ideas
- High Waisted Straight Leg Jeans With Split
